Computers purchased this fall from manufacturer Lenovo could have a root certificate called Superfish installed on them. This certificate belongs to the product Superfish, a preinstalled adware directing ads to the user by analyzing images and text on the websites you’re visiting.
It is possible to install a root certificate on any computer and then let the software create valid certificates for websites, since software can’t read traffic that’s being transported through HTTPS. This way, the software has access to the private keys and the password that is required to analyze the traffic.
This means that you are not safe just because you are visiting a website using HTTPS. Superfish can easily analyze that traffic, and since the main password for the root certificate has been cracked, anyone can set up a website with Superfish and your browser will show that the certificate is valid. This is also possible for man-in-the-middle attacks.
If you are connected to OVPN, you are protected against local attacks. Since OVPN is encrypting traffic, it is impossible to analyze the traffic in the same network. Still, though, it is possible to create certificates to any domain that your computer will show as legitimate, giving you a false sense of security.
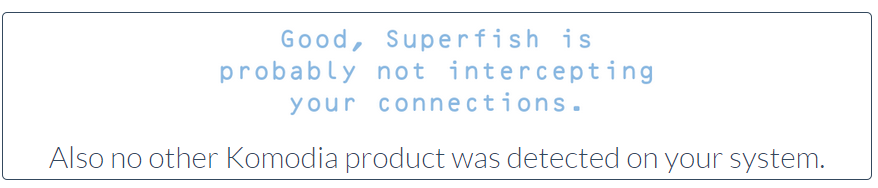
That is why we are asking everyone to make sure that you don’t have this certificate installed by visiting this website: https://filippo.io/Badfish/. You will get the following result if you are safe:
Please check all your browsers and computers. If you are affected, you can download a tool from Lenovo that removes the certificate: http://support.lenovo.com/us/en/product_security/superfish_uninstall

